Let agents act,
without losing control.
ifivo is the runtime control plane for AI agents. See what they do, approve what matters, and stop them instantly — with audit-grade logs across every tool, API, and payment rail.
curl -X POST https://www.ifivo.com/api/gateway/actions \
-H "content-type: application/json" \
-d '{
"agent_api_key": "sk_live_…",
"vendor": "stripe",
"action": "refund",
"amount_cents": 22000,
"risk_score": 0.55
}'
# → { "decision": { "outcome": "pending_approval",
# "reason": "Refunds over $150 require approval" } }/api/gateway/actions runs in the public simulator.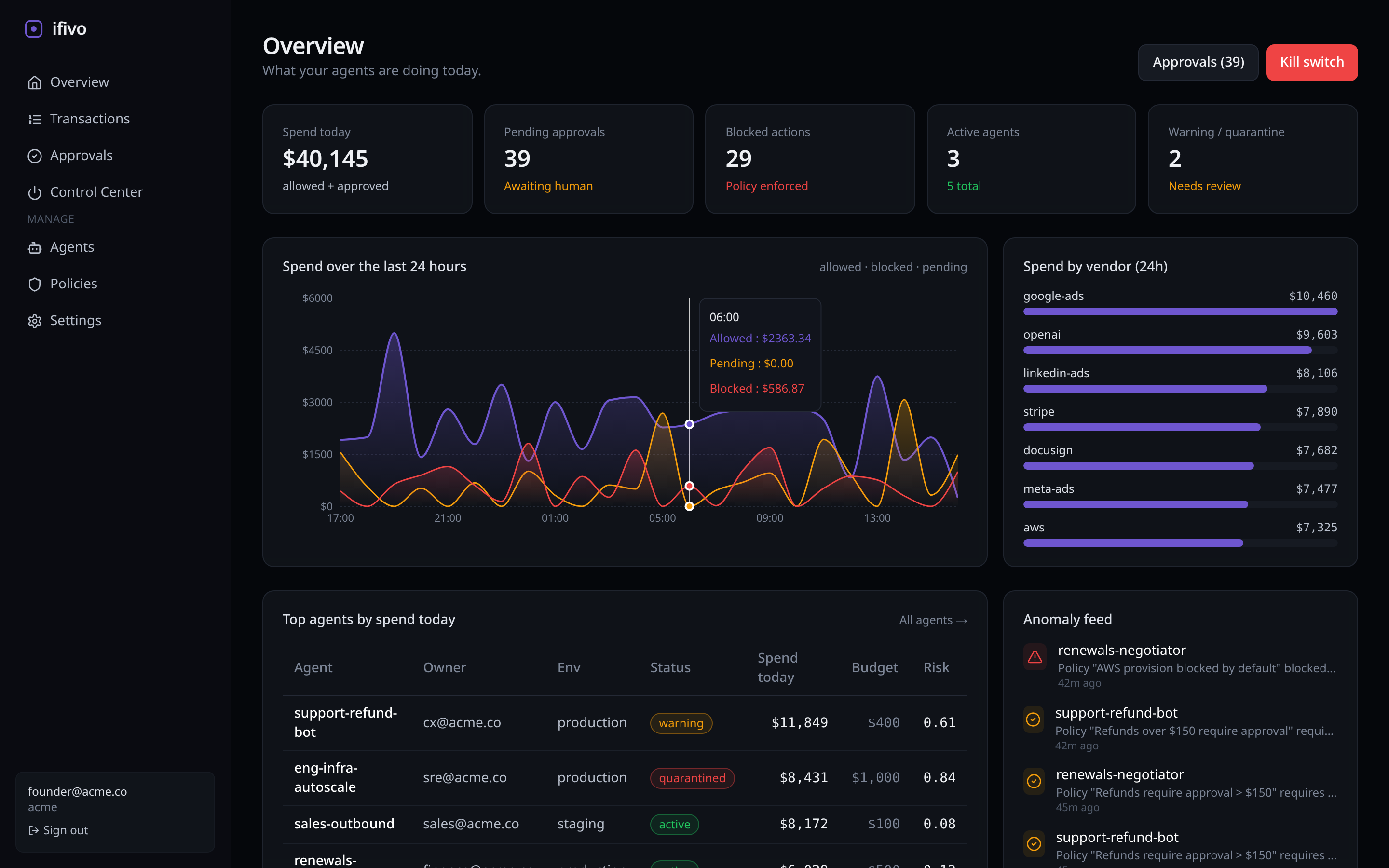
Four screens. One command center.
See the money, approve the risky moves, and shut it all down instantly. ifivo turns scattered agent logs into an operational control plane your security, finance, and engineering teams actually use.
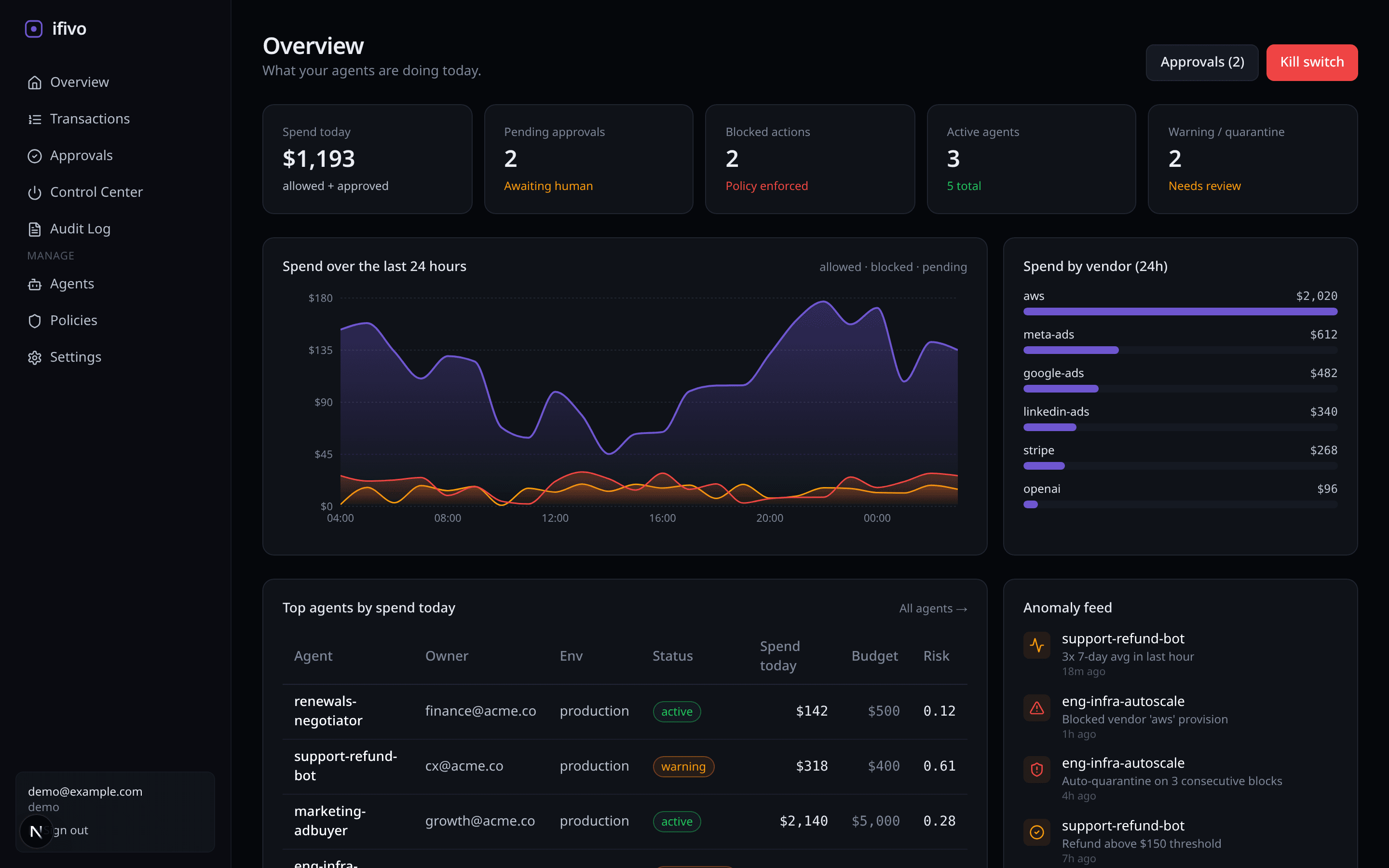
Overview
Daily spend, pending approvals, blocked actions, active agents — all at a glance.
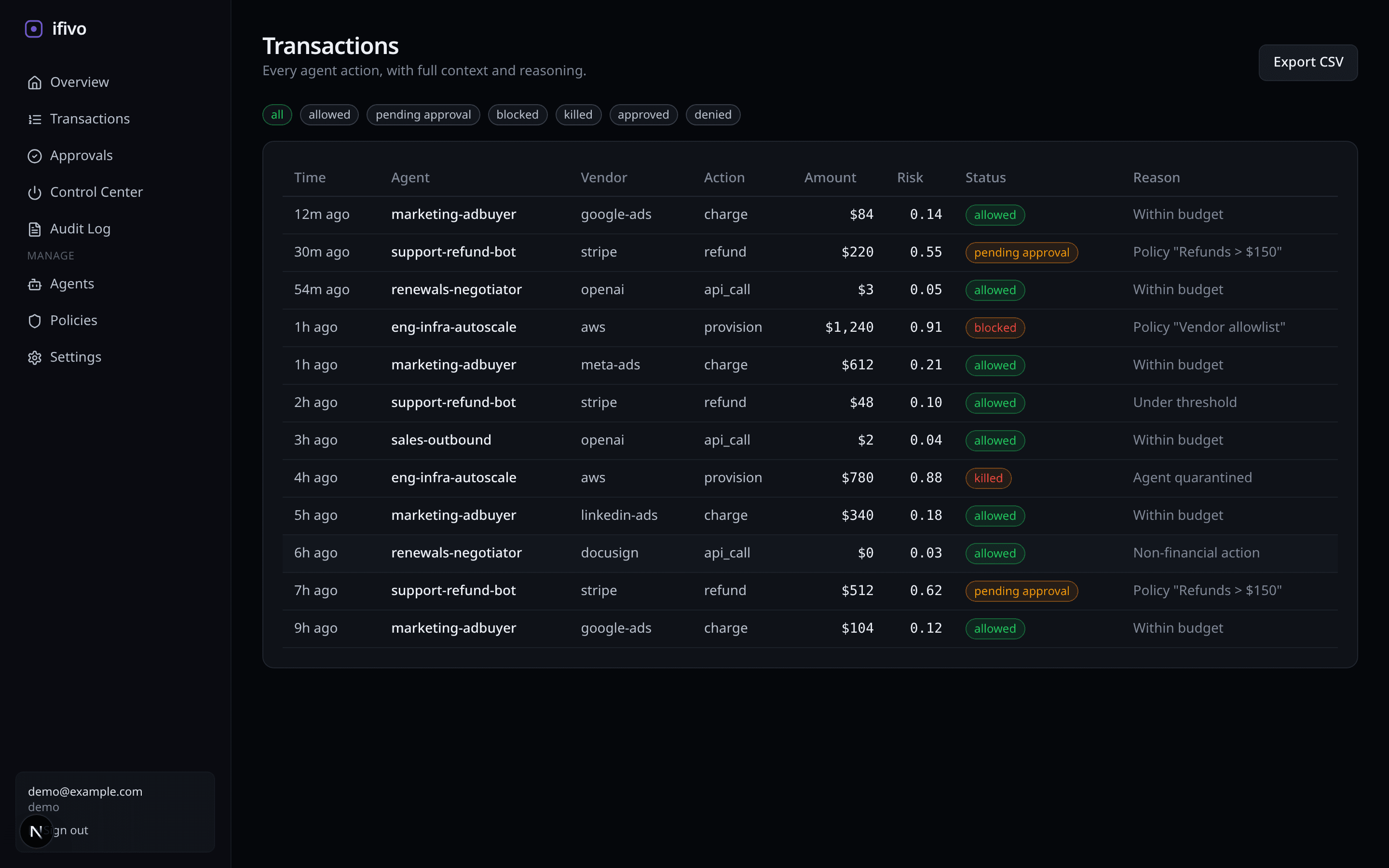
Transactions
Every agent action, filterable by vendor, policy, or risk — with full context.
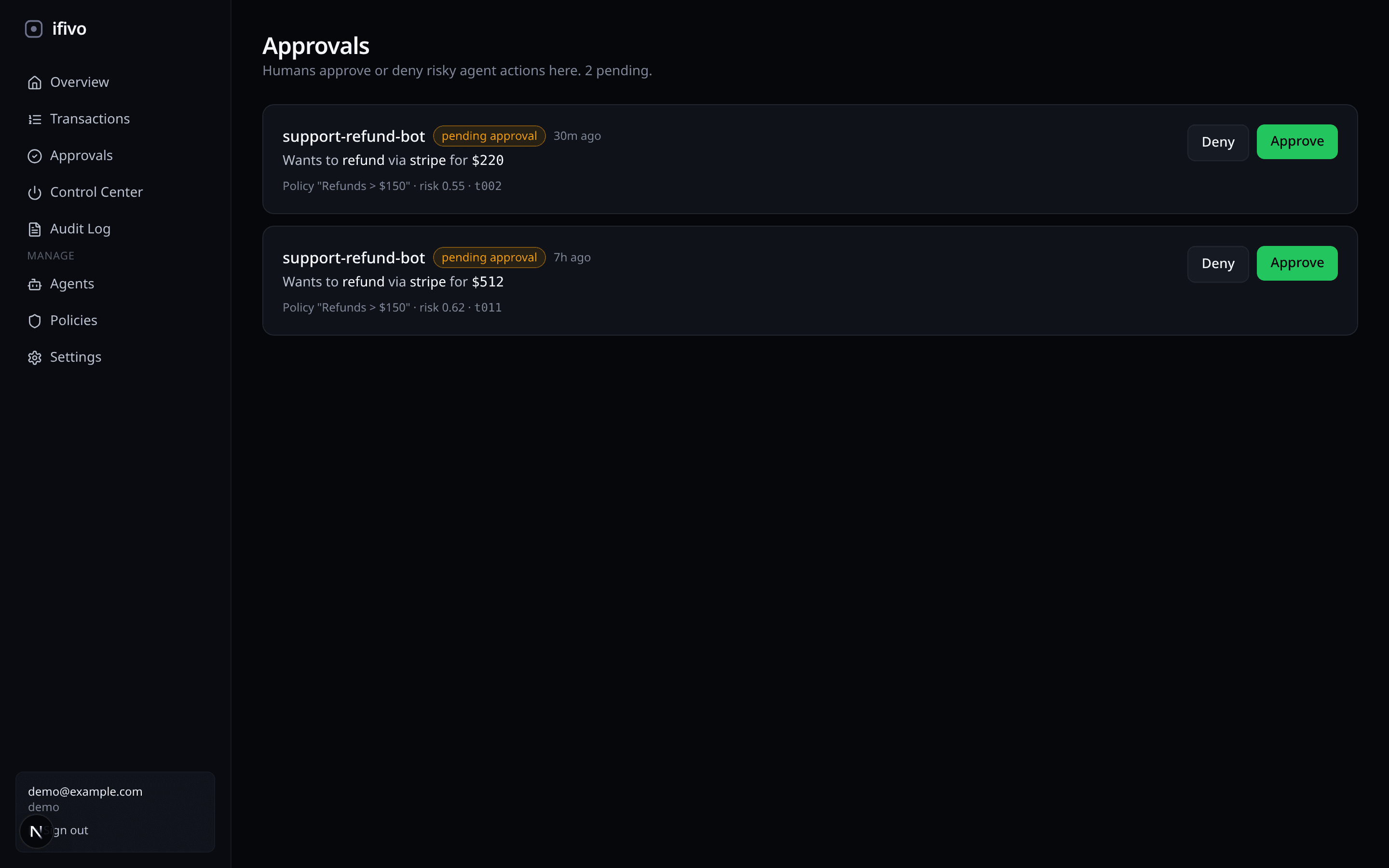
Approvals
Humans approve or deny high-risk moves from a single queue, or from Slack.
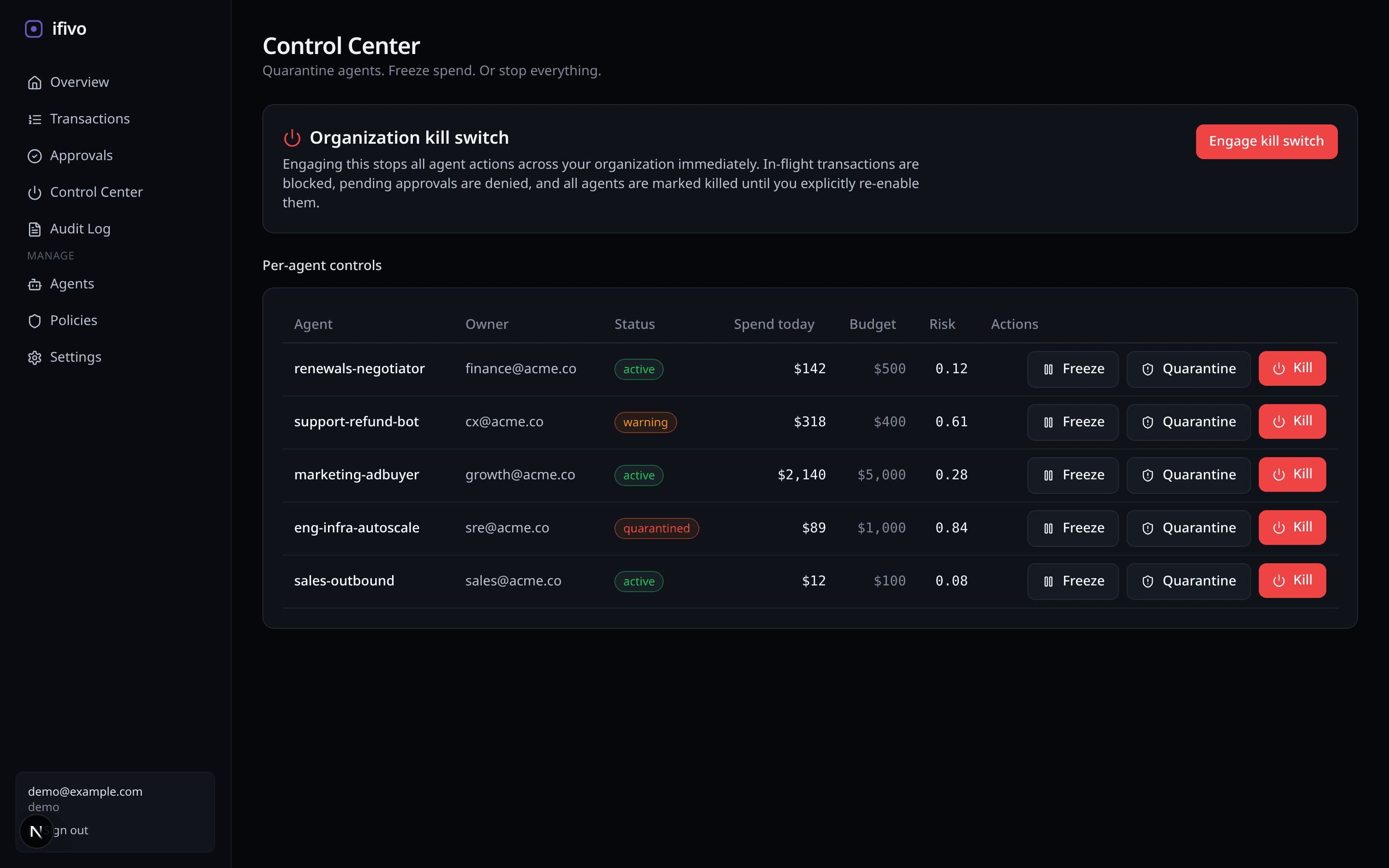
Control Center
Quarantine an agent. Freeze a budget. Or hit the org-wide kill switch.
See → Control → Intervene → Contain
See
Route agent actions through ifivo. Every call and payment attempt is logged with identity, intent, and risk.
Control
Define budgets, vendor allowlists, and risk thresholds. Deterministic rules run at the edge — no LLM required.
Intervene
Send anything above threshold to a human. Approve in-app or via Slack/email. Full diff of what the agent intended.
Contain
Quarantine an agent, freeze spend, or pull the org-wide kill switch. Authority is always revocable.
Roll out policy without touching traffic.
Run new rules in shadow for a week. Watch what would have been blocked, approved, or flagged, then tune the thresholds against real agent behavior. Flip to enforcement when the numbers look right — no surprise incidents at 2 a.m.
- Observe. Shadow policies log decisions without changing the outcome.
- Diff. Every transaction shows the live decision next to the shadow decision.
- Tune. Adjust thresholds in the policy editor, keep logs.
- Enforce. Flip the switch when you're confident.
shadow: false. 82 would-be approvals will start going to the approvals queue.Simple pricing. Ship today.
Start free. Upgrade when your agents touch real money.
Starter
For early pilots
- 1 org · 5 agents
- 10k actions / month
- Shadow mode + dashboards
- Community Slack
Team
Most popularFor production agents
- Unlimited agents
- 500k actions / month
- Approvals + kill switch
- SSO · audit export
- Email & Slack approvals
Enterprise
For regulated orgs
- SOC 2 / ISO artifacts
- On-prem gateway option
- Custom policy rules
- Dedicated support
- Stripe MPP + TAP integrations
Straight answers to the common questions.
How is this different from LangSmith, Arize, or Helicone?+
Do I need to route 100% of agent traffic through ifivo?+
What latency does the gateway add?+
Does Shadow Mode affect production behavior?+
What counts as an action?+
Can I self-host?+
How do I define policies?+
What happens when the kill switch is triggered?+
blocked from the gateway until a human releases it. Individual agents can also be quarantined without touching the org-wide switch.